Deep inside COBIT
For many enterprises, information and the technology that supports it represent their most valuable assets. Activities to protect these assets, management of IT risks and control over information constitute the core of IT governance. IT governance is the responsibility of the management and consists of the leadership, organizational structures and processes. It helps to ensure that IT supports the business objectives and can take full advantage of its information. COBIT is considered to be the main framework for IT governance because it is aligned with other standards and continuously improved.
IT Governance has become significant due to a number of factors:
- The consecutive pressure to save money demands for efficient IT processes
- Better return on IT investments (ROI) – deliver what customers needs
- A increasing number of laws and regulations demanding for IT and security management
- Trends such as Outsourcing and Off shoring
- Increasingly complex IT-related risks and a shifting threat landscape
Connected and aligned with business
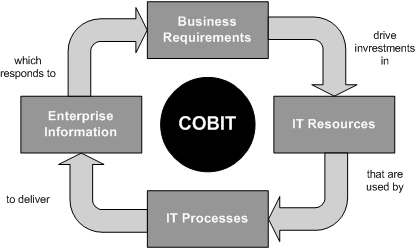
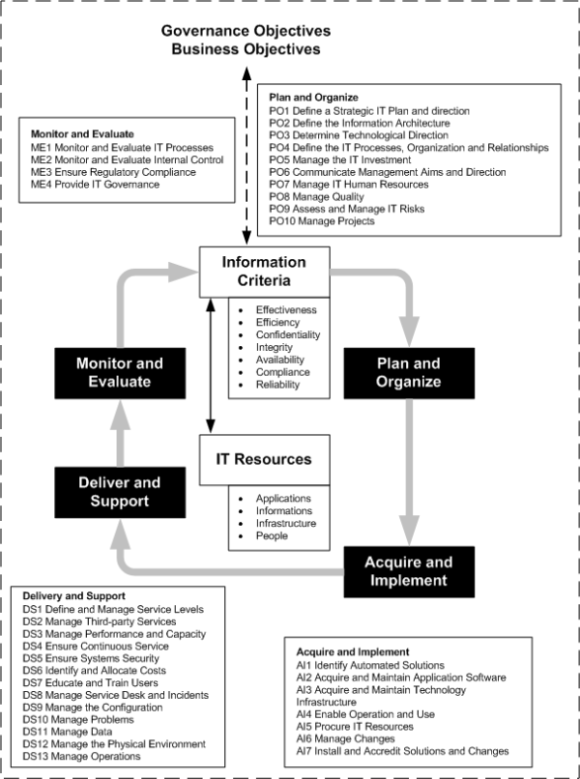
COBIT contributes making the IT able to deliver against the business requirements by linking IT with the business, organizing activities into a accepted process model, identifying the major IT resources to be leveraged and defining control objectives and process controls. Business orientation is the main theme of COBIT.
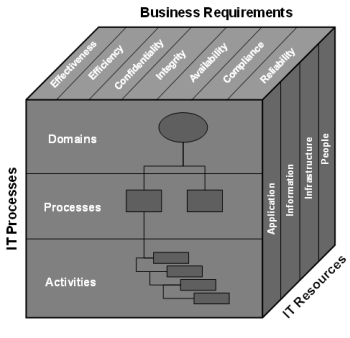
Managing and controlling information are at the heart of the COBIT framework and help ensure alignment to business requirements. In order to conform with certain control criteria (the business requirements for information), COBIT defines seven information criteria:
- Effectiveness - deals with information being relevant and pertinent to the business process as well as being delivered in a timely, correct, consistent and usable manner
- Efficiency - the provision of information through the optimal (most productive and economical) use of resources
- Confidentiality - the protection of sensitive information from unauthorized disclosure
- Integrity - the accuracy and completeness of information as well as to its validity in accordance with business values and expectations
- Availability - information being available when required by the business process now
- Compliance - complying with the laws, regulations and contractual arrangements
- Reliability – the provision of appropriate information for management to operate the entity
Business and IT goals
COBIT’s business orientation is reflected by deriving IT goals form the business objectives while taking business into account. If IT is to successfully deliver services to support the enterprise’s strategy, there should be a clear ownership and direction of the requirements by the business and a clear understanding of what needs to be delivered, and how, by IT.
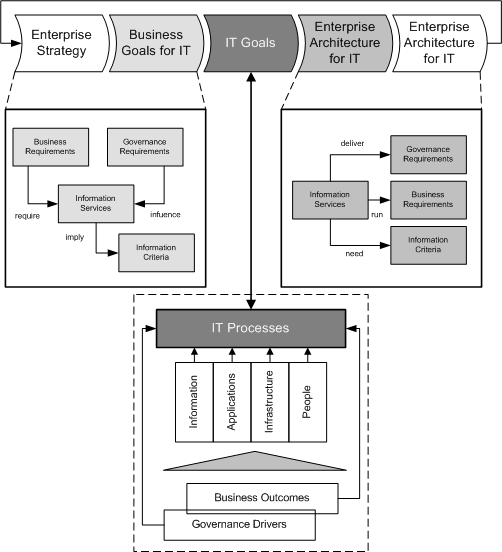
Goals that have been aligned and agreed on need to be monitored to ensure the delivery matches expectations. This is achieved by metrics that are derived from the goals and captured in an IT scorecard. For the customer to understand the IT goals and IT scorecard, all of these objectives and associated metrics should be expressed in business terms meaningful to the customer. To do so helps to ensure that the customer can confirm that the IT is likely to support business.
The IT organization delivers against the IT goals by a clear set of effective and efficient IT processes, supported by a variety of resources, such as:
- Infrastructure
- Applications
- Information
- Staff
Resources and criteria are shown in the COBIT cube.
Process oriented
COBIT’s process focus is illustrated by having 34 major processes organized in four domains.
In order to get IT under control such that it delivers desired output, COBIT:
Defines activity goals by setting control objectives
- Tool: Dashboard
- Outcome: Indicators
Measures process performance by using a balance scorecard
- Tool: Scorecard
- Outcome: Measures
Benchmarks performance and capability by applying the Capability Maturity Model (CCM)
- Tool: Benchmarking
- Outcome: Scales
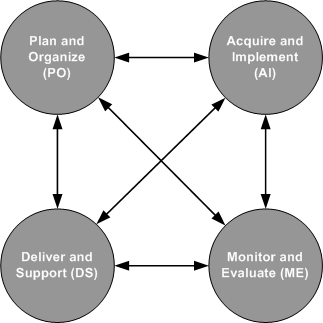
Plan and Organize (PO)
Strategy definition, tactics and planning take place in this domain. It concerns the way IT can best contribute to the business objectives.
Acquire and Implement (AI)
This domain covers the evaluation, acquisition and development of IT solutions, who need to be implemented and integrated to realize the IT strategy. This domain covers also changes maintenance and changes of existing systems.
Deliver and Support (DS)
This domain is concerned with service delivery and service delivery management, support, security, continuity management, management of data and operating facilities.
Monitor and Evaluate
To measure performance, IT processes need to be assessed over time for quality and performance. This domain addresses performance management, monitoring of internal control, regulatory compliance and governance.
Across these four domains, COBIT has identified 34 IT processes that are generally used.
Verified by Controls
Control is defined as the policies, procedures, practices and organizational structures designed to provide reasonable assurance that business objectives will be achieved and undesired events will be prevented or detected and corrected. Effective controls reduce risk, increase the likelihood of value delivery and improve efficiency because there will be fewer errors and a more consistent management approach.
Control objectives
Control objectives provide a complete set of high-level requirements to be considered by management for effective control of each IT process. Because each COBIT process has a number of control objectives defines by default, it is important to select those that are applicable and decide upon which ones to implement. The control objectives are identified by a two-character domain reference (PO, AI, DS and ME) plus a process number and a control objective number.
Beside the already mentioned control objectives, COBIT defines overarching process and application controls.
Process controls
In addition to the control objectives, each process has a number of process controls, which should be considered together with the control objectives to get a complete view. The process controls are:
PC1: Process Goals and Objectives
- Definition of process goals and objectives (SMART)
PC2: Process Ownership
- Assignment of an owner for each IT process including tasks and responsibilities
PC3: Process Repeatability
- Processes shall be designed in a way that it is repeatable and consistently produces the expected results
PC4: Roles and Responsibilities
- Main deliverables of the process and necessary roles to operate it
PC5: Policy, Plans and Procedures
- Life cycle management of constitutional documents
PC6: Process Performance Improvement
- Definition of metrics, how to obtain data and how to measure
In addition to know what controls to select, process owners need to understand what inputs they require from others and what others require from their process. COBIT provides illustrative examples for each process in the sections of:
- Input and Output
- Activities
- Roles and Responsibilities
- RACI
- Activity goals
- Metrics
- Maturity status
The examples meant not to be exhaustive but give you a good idea and direction. You have to adapt them, choose the ones that are applicable and decide upon which controls to implement.
A companies system of internal controls impact the IT at three levels:
- Executive management level– this is where business objectives are set, policies established and decisions are made on how to deploy and manage the resources.
- Business process level - controls are applied to specific business activities. Most business processes are automated and integrated with IT application systems - these controls are known as application controls. However, some controls within the business process remain as manual procedures. Therefore, controls at the business process level are a combination of manual controls operated by the business and automated business and application controls. Both are the responsibility of the business to define and manage, operating of the application controls is in the obligation of the IT.
- IT service level – IT provides services to support the business. The controls applied to all IT service activities are known as IT general controls (e.g., problem-, change- and release mgmt). The reliable operation of these general controls is necessary for reliance to be placed on application controls.
Application controls
The following list provides a recommended set of application control objectives:
AC1: Source Data Preparation and Authorization
- Ensure that source documents are prepared by authorized and qualified personnel following established procedures, taking into account adequate segregation of duties. Errors and omissions can be minimized through good input form design
AC2: Source Data Collection and Entry
- Establish that data input is performed in a timely manner by authorized and qualified staff
AC3: Accuracy, Completeness and Authenticity Checks
- Ensure that transactions are accurate, complete and valid
AC4: Processing Integrity and Validity
- Maintain the integrity and validity of data throughout the processing cycle
AC5: Output Review, Reconciliation and Error Handling
- Establish procedures and associated responsibilities to ensure that output is handled in an authorized manner, delivered to the appropriate recipient, and protected during transmission
AC6: Transaction Authentication and Integrity
- Before passing transaction data between internal applications and business functions, check it for proper addressing, authenticity of origin and integrity of content
Altogether these controls help to assure completeness, accuracy and validity of data, authorize access to it and support segregation of duties.
Evolvement determination by maturity models
Prior on acting and improving, a company needs to know the status of its processes, IT systems and controls. While this sounds easy, it is not in praxis, it assumes what to measure and how. COBIT deals with these issues by providing maturity models to enable benchmarking and identification of necessary capability improvements. The maturity model used in COBIT is shown below.
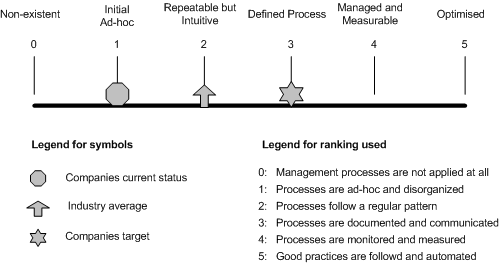
Using the maturity model developed for each of COBIT’s 34 IT processes, management can identify:
- “As is”: The actual performance of the company
- “Comparison”: The current status of the industry
- “To be”: The companies target for improvement
- “Path”: The required growth path between “as-is” and “‘to-be”
Please be aware that when assessing a process, implementation parts of a process can be at different levels. This means that one part can be not sufficient while others are. You can reflect such a state for example in a clustered column chart.
The 0-5 scale is based on a simple maturity scale showing how a process evolves from a non-existent capability to an optimized capability.
- 0. Non-existent - complete lack of any recognizable processes. Responsible do not even know that there should be something in place
- 1. Initial / ad hoc - the company has recognized that the issues exist and need to be addressed. However, there are no standardized processes in place but ad hoc approaches. Overall not very organized
- 2. Repeatable but Intuitive – Can be referred as where similar procedures are followed by different people undertaking the same task, with a high degree of reliance on the knowledge of individuals. No training or communication of standard procedures, and responsibility is left to the individual
- 3. Defined Process - procedures have been standardized and documented, and communicated through training. Staff is expected to follow these, however, it is unlikely that deviations will be detected
- 4. Managed and Measurable – processes and procedures are managed and monitored on a continuous basis and corrected where is evidence that not be working effectively and efficiently. Processes are under constant improvement and provide good practice. However, automation and tools are used in a limited or fragmented way
- 5. Optimized - processes have been developed to a level of good practice, based on the results of continuous improvement and maturity modeling with other enterprises. IT is used in an integrated way to automate the workflow, providing tools to improve quality and effectiveness. Overall, the company is able to react quickly on changes
The three maturity dimensions (of a process) can be illustrated as follows:
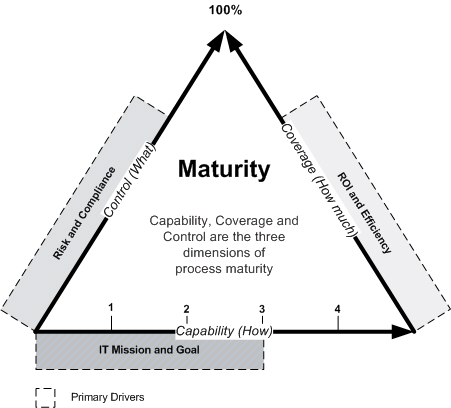
The maturity model is a way of measuring, explain and express how well developed management processes are, i.e., how capable they actually are. How well developed or capable they should be primarily depends on the IT goals and the underlying business needs they support.
Be aware that process management capability is not the same as process performance. Capability, as determined by business and IT goals, may not need to be applied to the same level across the entire IT environment, e.g., not consistently or to only a limited number of systems or units.
The maturity models used in COBIT are built up starting from the generic qualitative model (capability ranking 0-5) to which principles from the following attributes are added in an increasing manner through the levels:
- Awareness and communication
- Policies, plans and procedures
- Tools and automation
- Skills and expertise
- Responsibility and accountability
- Goal setting and measurement
Characteristics from the above attributes are used to describe how IT processes are managed and how they evolve from a non-existent to an optimized process.
In summary, maturity models provide a generic procedure to assess, elaborate and display the capability of IT processes and how they evolve over time. Coverage, depth of control, and how the capability is used and deployed are cost-benefit decisions.
Although a properly applied capability already reduces risks, an enterprise still needs to analyze the controls necessary to ensure that risk is mitigated and value is obtained in line with the risk appetite and business objectives. These controls are guided by COBIT’s control objectives.
Performance Measurement
Goals and metrics are defined in COBIT at three levels:
IT goals and metrics
- Business expectations on IT and how to measure it
Process goals and metrics
- What the IT process must deliver to support IT’s objectives and how to measure it
Activity goals and metrics
- What needs to be done to achieve the required performance and how to measure it
See in the graphic below how different kinds of goals are linked together.
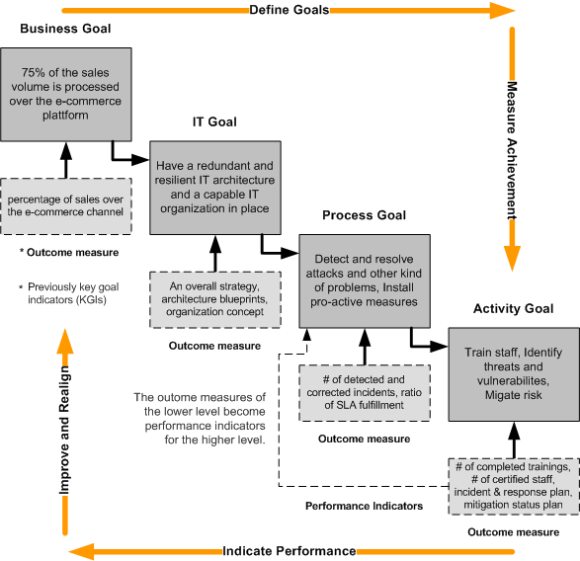
Outcome measures indicate whether goals have been met. The question can be answered only after the fact, so they are called “lag indicators”.
Performance indicators indicate whether goals are likely to be met. They are called “lead indicators”, because they can be applied before the outcome is clear.
Outcome measures of IT functions are often expressed in terms of information criteria, such as:
- Availability of information
- Breach of integrity and confidentiality
- Confirmation of reliability, effectiveness and compliance
- Proof of cost efficiency
COBIT provides outcome measures for the areas of “IT Goal” up to “Activity Goal”. While IT outcome measures can serve as performance indicators for business goals, COBIT itself does not provide outcome measures for business goals.