ISO 27001:2005
- Scope
- Normative references
- Terms and definitions
- Information security management system
- Management responsibility
- Internal ISMS audits
- Management review of the ISMS
- ISMS Improvement
Annex
ISO 27001 has been prepared to provide a model for establishing, implementing, operating, monitoring, reviewing, maintaining and improving an Information Security Management System (ISMS). ISO 27001 is applicable to any organization, regardless of size, type or nature. The way an organization builds an ISMS should be a strategic decision. The ISMS is influenced by an organization’s need, objectives, security requirements and its size and structure.
ISO 27001 adopts a process to build an Information Security Management System. The ISMS is designed to ensure the selection of adequate and proportionate security controls that protect information assets and give confidence to interested parties. Prior it is important to understand the importance of:
- An organization’s information security requirements
- Implementing and operating controls to manage that organization's information security risks
- Monitoring and reviewing the performance and effectiveness of the ISMS
- Continual improvement based on objective measurement
ISO 27001 adopts the "Plan-Do-Check-Act" (PDCA) model.
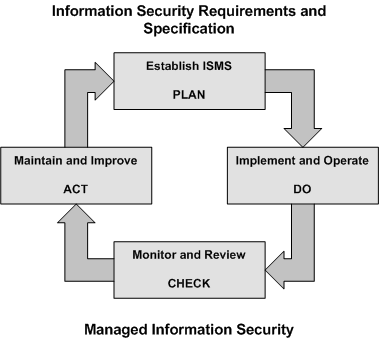
Establishing and managing the ISMS
Establish the ISMS
First step is to establish the ISMS. This is done by defining scope and boundaries of the ISMS, in respect to organization-specific characteristic. The ISMS policy needs to be defined, as well a the risk assessment approach of the organization, which is part of the ISMS policy.
Next steps are all about risk management. The organization must identify, analyze and evaluate the risks. This is done by assessing the business impacts upon the organization that might result from security failures. Upon this, options for the treatment of risks must be considered. Part of this is the selective choice of control objectives and controls. Control objectives and controls must be selected and implemented to meet the requirements identified by the risk assessment and risk treatment process. Keep in mind that activities must be compliant with the amount of risk the organization is willing to take (risk strategy – risk appetite). Once all identified risks have been counter measured, management must approve residual risk.
We know now why, how and what to do, management must now authorize implementation and operating of the ISMS. This also assures resources (time, money, staff …) are available to do so.
An important step is to prepare the Statement of Applicability (SoA). The SoA is a documented statement describing the control objectives and controls that are relevant and applicable to the organization’s ISMS. The controls and objectives are derived from ISO 27002.
Implement and operate the ISMS
The risk treatment plan needs now to be finished with tasks, responsibilities and priorities for managing information security risks. It is one of the most important steps to achieve management commitment for the whole security program. When done, the risk treatment plan with its controls must be implemented in order to achieve control objectives.
An organization should also consider establishing a performance management framework with proper metrics to measure effectiveness of the controls. This allows determining how well controls achieve planned control objectives.
Training and awareness programs and a process for prompt detection of security events and response to security incidents is also required and part of the implement and operating phase.
Monitor and review the ISMS
Implemented controls should be permanently monitored to detect processing errors, as well as attempted and successful security breaches and incidents. This also helps to verify the effectiveness of the security organization. The ISMS must undergo regular reviews to determine effectiveness. This includes policy, controls and objectives, lessons learnt from incidents, feedback and suggestions from interested parties.
Results from risk assessments should be reviewed at regular intervals to comply with the shifting threat landscape. This is to assure the residual risk is still consistent with the risk treatment regulations.
The ISMS should be audited at regular intervals. Update security plans to take into account the findings of monitoring, reviewing and auditing activities.
Maintaining and improving the ISMS
In order to maintain and improve the ISMS, improvements, corrective and preventive actions, derived from the regular updated security plans, must be implemented. Do not forget to take the lessons learnt into account. Ensure that the improvements achieve their indented objects. Communicate improvements to all interested and affected parties.
Documentation requirements
Implementing and establishing an ISMS requires some documentation work. The ISMS documentation should include at least:
- Scope of the ISMS
- Statements of the ISMS policy
- Procedures and controls
- Risk assessment methodology
- Risk treatment plan
- Statement of Applicability (SoA)
Documentation should also include management decisions to ensure actions are traceable and results reproducible. This sounds after a lot of documentation work, but keep in mind that size and complexity of the ISMS depends on an organization’s need, size and structure.
Documents required by the ISMS should be protected and controlled. This includes approval, review, update, versioning, distribution and so on. Records must be established and maintained to provide evidence of conformity to requirements and the effective operation of the ISMS.
Management responsibility
Management commitment
Management must give its commitment for the ISMS by establishing a policy, provide sufficient resources to launch and operate the ISMS, establishing roles and responsibilities, decide upon criteria for risk management, ensure that audits are conducted and perform management reviews of the ISMS.
Resource management
The ISMS managers must determine necessary resources to establish and run the ISMS, whereas it is in the obligation of the management to provide them. Resources are needed to establish, implement, operate, monitor, review, maintain and improve an ISMS and to ensure that business, legal and regulatory requirements are met. The organization must ensure that all personnel who are assigned responsibilities defined in the ISMS are competent to perform the required tasks. This is done by training and awareness. However, for a security program to be effective, an organization must provide training and awareness services beyond security organization boundaries
Internal ISMS audit
The ISMS must undergo regular audits to determine whether it operates as expected and effectively according to the identified security requirements. The responsibilities and requirements for planning and conducting audits, and for reporting results and maintaining records should be defined in a documented procedure.
Management review of the ISMS
The ISMS is monitored continuously and audited at regular interval to ensure its effectiveness and efficiency. Alongside, management should support these efforts by assessing opportunities to improve and change the ISMS. This also included review of the information security policy and security objectives. Results must be clearly documented and recorded.
To do so management can use results from reviews and audits, feedback from interested parties, indicators from performance management (effectiveness management), lessons learnt and status form preventive and corrective actions.
Output from the management review should include decisions and actions to improve the effectiveness of the ISMS, update risk assessment and treatment plan and finally modification of procedures and controls that effect information security as needed due to the shifting threat and requirements landscape.
ISMS improvement
An organization must continually improve the effectiveness of the ISMS through the use of the information security policy, security objectives, review and audit results, analysis of monitored events, performance management framework, corrective / preventive actions and finally management review.
Annex ISO 27001
Statement of applicability
The control objectives and controls for ISO 27001:2005 are directly derived from and aligned with those listed in ISO 17799:2005. An organization may consider that additional control objectives and controls are necessary. Control objectives and controls shall be selected as part of the ISMS process specified in 4.2.1. Altogether they make the “Statement of Applicability” SOA.
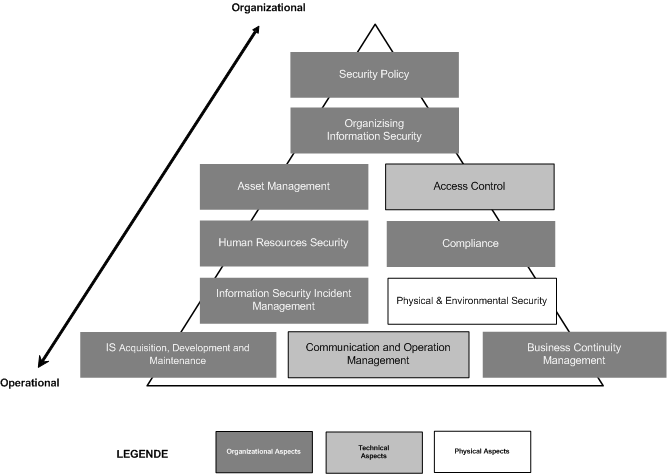
Statement of Applicability
The Statement of Applicability is the documented statement describing the control objectives and controls that are relevant and applicable to the organization’s ISMS. Be aware that control objectives and controls must be based on the results and conclusions of the risk assessment and risk treatment processes, legal or regulatory requirements, contractual obligations and the organization’s business requirements for information security.
The SOA is created as follows:
- Go trough all controls (133 as of version 2005)
- Decide whether applicable or not
- Justify why so
- Search for procedure / measure
- Reference procedure / measure in the SOA or describe it
- Document status of each control
You can use the following approach to document the status of each control:
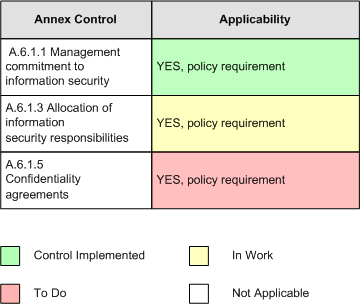
Trough the use of colors the status of measures is now easily visible.
Example of an ISMS TOC
INTRODUCTION
- Objective
- Contents
- Approval and Distribution Policy
ISMS SCOPE
ISMS POLICY
- Risk Management
- Assets
- Business Objectives
- Risk Evaluation Criteria
- Management
- Personnel Policies
- IT
- Forensic
- Documentation
- Other applicable policies
- Certification
INFORMATION SECURITY CONTEXT
- Architecture
- Security perimeter
- Assets
- Threat agents
- Summary of adverse impact
RISK ASSESSMENT AND RISK TREATMENT
- Approach
- Risks concerning business
- Risks concerning theft
- Risks concerning acts of god, vandals and terrorist
- Risks concerning regular fraud
- Risks concerning IT failure
- Risks concerning hacking
- Risks concerning denial of service
- Risks concerning disclosure/misuse of classified information
- Risks concerning law
STATEMENT OF APPLICABILITY
Index
- Index
- Security policy
- Information Security Policy
- Organization of information security
- Internal Organization
- External Parties
- Asset management
- Responsibility for Assets
- Information Classification
- Human resources security
- Prior to employment
- During employment
- Termination or change of employment
- Physical and environmental security
- Secure Areas
- Equipment Security
- Communications and operations management
- Operational Procedures and Responsibilities
- Third Party Service Delivery Management
- System Planning and Acceptance
- Protection against Malicious and Mobile Code
- Back-up
- Network Security Management
- Media handling
- Exchange of Information
- Electronic Commerce Services
- Monitoring
- Access control
- Business Requirement for Access Control
- User Access Management
- User Responsibilities
- Network Access Control
- Operating System Access Control
- Application and Information Access Control
- Mobile Computing and Teleworking
- Information systems acquisition, development and maintenance
- Security Requirements of Information Systems
- Correct Processing in Applications
- Cryptographic Controls
- Security of System Files
- Security in Development and Support Processes
- Technical Vulnerability Management
- Information security incident management
- Reporting Information Security Events and Weaknesses
- Management of Information Security Incidents
- Business continuity management
- Information Security Aspects of Business Continuity
- Compliance
- Compliance with Legal Requirements
- Compliance with Security Policies and Standards
- Information Systems Audit Considerations
ISMS METRICS AND INCIDENT HANDLING
- Introduction
Time theory- Fundamental Principle
- Plan-Do-Check-Act
- Incidents and Impacts
- Impact log
INCIDENT HANDLING PROCEDURE
- Incident Identification and Reporting
- Incident Handling and Escalation
- Communicating Results and Tidying Up
MONITORING CONTROLS
- Check Activities
- Other Metrics
TRAINING AND AWARENESS
OTHER PROCEDURE HANDBOOKS AND MANUALS
DOCUMENT CONTROL
- Introduction
- Document control records
- Change control
- Introduction
- The Change Control Process
- Change Control Procedure
- Document review
- Structural Review
- Technical Review
- Presentation Review
BUSINESS CONTINUITY PLAN
- The Management Process
- Impact Analysis
- The Plan
- Testing
CHECK AND ACT
- General activities
- Special activities
- Internal ISMS audit
- Schedule
- Objectives
- Non-conformities
- Internal ISMS Audit Report and Checklist
- Audit Conduct
- Management review
- Schedule
- Objectives
- Management Review Checklist
- Continual improvement
- Corrective Action
- Preventive Action
RECORDS AND DOCUMENT CONTROL
- Control of ISMS records
- Control of documents
- To do list